Ticker
Ad Code
Incident Management
What is meant by incident management? Incident management is a defined process for logging, re…
China New Crypto Ranking: Bitcoin Upgraded
The Center for Information and Industry Development (CCID), below China’s Ministry of Industry and …
Bitcoin Killer
In 2019, many Onecoin associates are being charged with crimes by law enforcement companies from multiple…
LendaBit.com Launches Excellent P2P Service
LendaBit, one of the quickest-growing P2P lending systems, is pleased to announce the launch of a brand ne…
KuCoin Launches Platform 2.0 With Advanced API
KuCoin, one of the maximum popular cryptocurrency exchanges, has formally released KuCoin Platform 2.0. …
Unique Email Marketing
Choosing the right e mail marketing carrier will have a considerable impact on the success of your marketing mar…
SEO Friendly URL Structure
What is a search engine marketing Friendly URL? Before we go too deep into WordPress permalinks, it’s essent…
Metasploit
GBHackers On Security Cyber Security NewsSecurity Hacker Metasploit Framework five.0 Released With New Evasio…
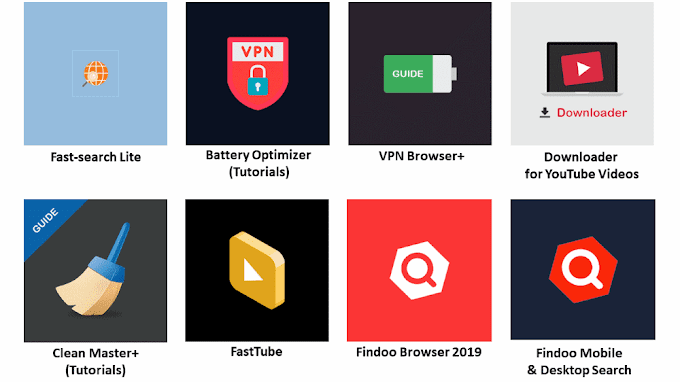
Cryptojacking Apps
Crypto jacking apps located on the Microsoft Store tha abuses victim’s CPU cycle to mine Monero with out user experti…
Abusing LinkedIn’s Direct Messaging Service
A new malware campaign that impersonates as legitimate staffing businesses abuse messaging offerings to deliver More_…
Banking Malware Through Fake Google reCAPTCHA
New malware campaign impersonates a fake Google reCAPTCHA to supply banking malware. The campaign especially targeted…
How To Protect Your Company
1. Screen Potential New Employees:- One of the high-quality approaches to save you insider threats from affecting…
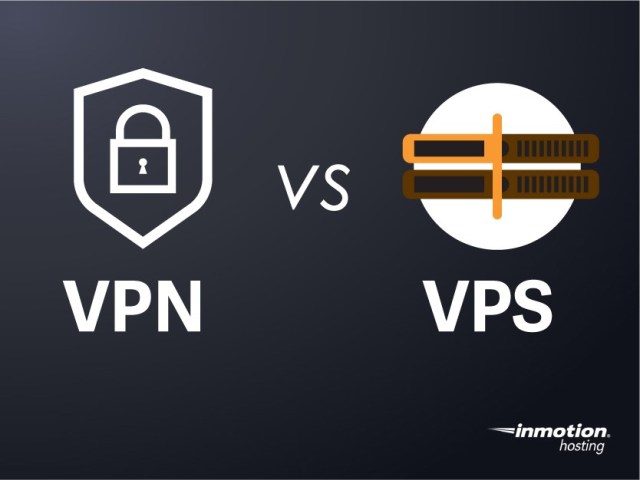
VPN on VPS safer
All the community visitors among your laptop and the VPS goes through an encrypted VPN tunnel, also the VPN on VPS ad…
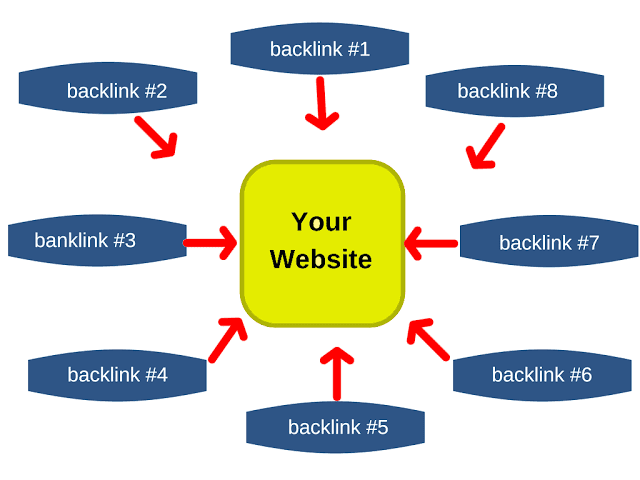
SEO Hacks You Need To Stop
Web entrepreneurs are regularly faced with a myriad of SEO challenges. Let’s say you have got determined to attention…
iPhone Remotely Monitoring Tool
We know this isn't always viable the usage of any default application at the iOS platform, we can’t ask Apple for…
CISA certification
The CISA certification is famend across the world as the standard of success for those who audit, reveal, get right o…
CISM Certification
The demand for professional statistics safety managers is on the upward push, and CISM is the globally frequent certi…
























Social Plugin